
Autonomous Pentest with AI
Offensive security for Web and APIs with the speed of AI
Autonomous AI-driven pentest that performs real attack simulations, identifies vulnerabilities, and delivers a severity-prioritized list, technical evidence with proof of concept, documented attack chains, and execution history for continuous re-testing.

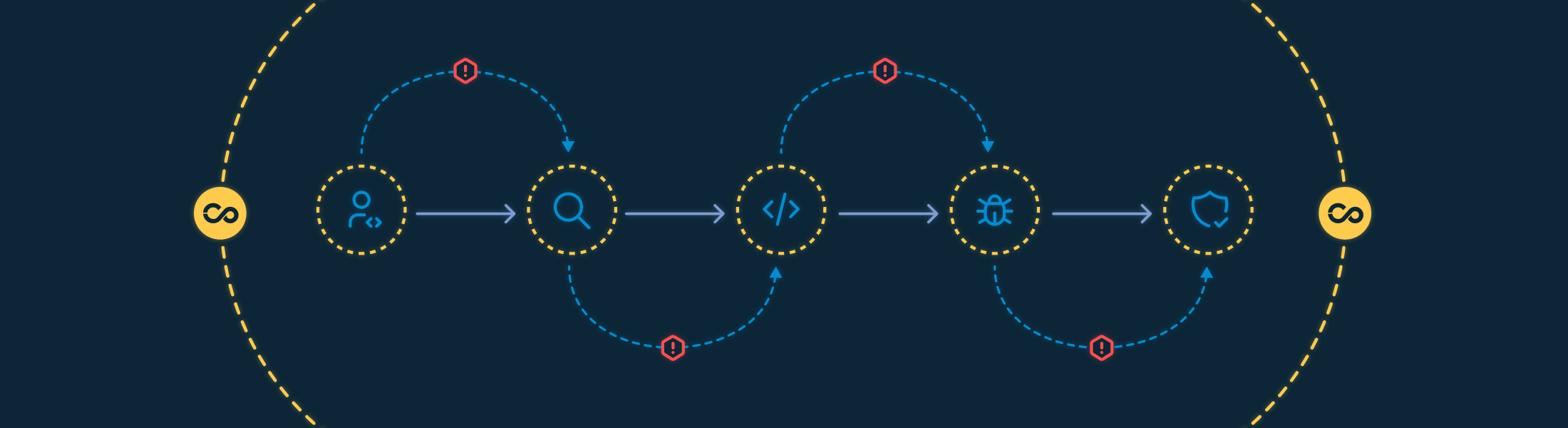
A dynamic attack surface requires continuous offensive validation
Modern development environments combine web applications, APIs, microservices, and external integrations. Each deployment changes the exposed surface and may introduce new attack vectors. Traditional scanners identify technical patterns. The market increasingly requires real exploitation validation and a clear demonstration of impact.
Today, companies face a common scenario:
Partial visibility into routes and endpoints that are actually exposed
Difficulty validating the exploitability of identified vulnerabilities
Lack of chaining between isolated vulnerabilities
Insufficient evidence for risk-based prioritization
Point-in-time testing that does not keep up with application evolution
A segurança que acompanha o ritmo da sua fintech
Unimos tecnologia, inteligência e consultoria Combinamos tecnologia, inteligência e consultoria para transformar vulnerabilidades em eficiência e conformidade contínua.para transformar vulnerabilidades em confiança e compliance contínuo.
Autonomous Pentesting begins by identifying the application’s effectively exposed surface. This phase consolidates accessible routes, active endpoints, communication patterns, and implemented controls. The goal is to structure a functional inventory of the application's behavior before exploring specific vulnerabilities.
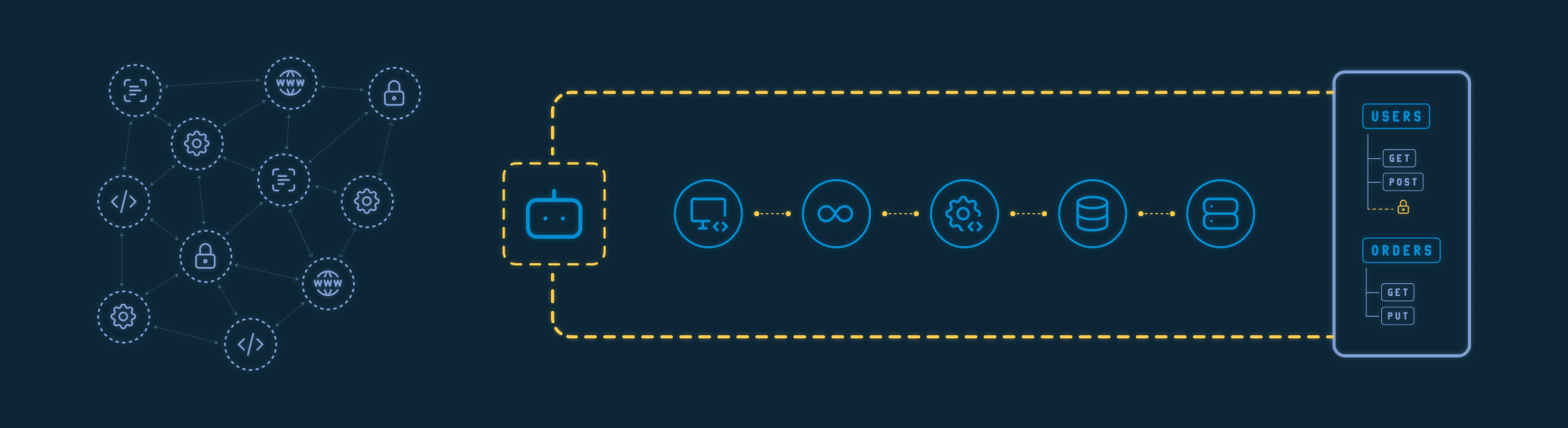
How we structure this stage

Identification of valid URLs and accessible routes

Mapping of API endpoints

Discovery of available HTTP methods

Analysis of accepted parameters, headers, and payloads

Identification of exposed surfaces and accessible resources

Observation of implemented authentication patterns
Direct impact
.svg)
Consolidated mapping of the attack surface
.svg)
Objective direction for exploitation attempts

Identification of routes and assets outside the expected scope
Environment configuration determines how the application responds, which controls are active, and which resources remain accessible. This stage evaluates the structural layer supporting the application—server configuration, applied policies, and exposed resources—to identify deviations that increase the attack surface.

How we analyze this layer

Evaluation of web server configurations

Verification of applied security policies

Identification of missing or misconfigured security headers

Detection of sensitive file exposure

Analysis of publicly accessible directories and resources
Direct impact

Identification of structural weaknesses
.svg)
Hardening-oriented remediation guidance

Reduction of unnecessary exposure
Authentication mechanisms control initial access to the application. This stage evaluates how identity is validated, how sessions are maintained, and which conditions may allow unauthorized access. The objective is to identify deviations that enable the use of invalid credentials, session reuse, or token manipulation.
How tests are conducted

Evaluation of login mechanism robustness

Credential validation tests

Session management analysis

Evaluation of authentication tokens, such as JWT

Verification of session expiration and renewal
Direct impact

Identification of vulnerabilities allowing unauthorized access

Exposure of weaknesses in session management

Foundation for improving authentication and identity control policies
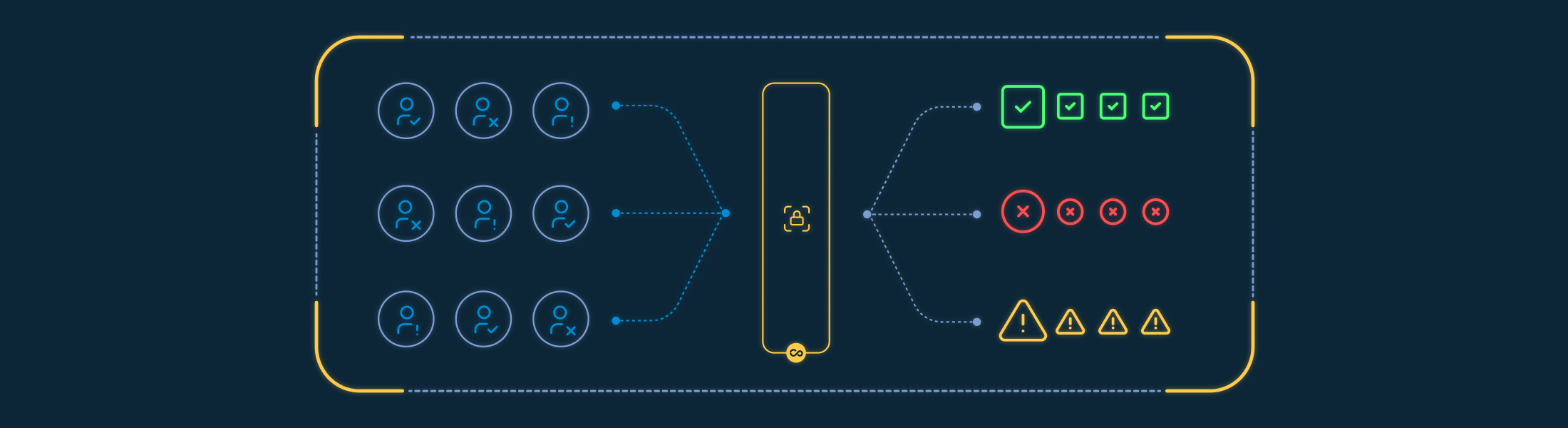
After authentication, authorization determines which actions each user can perform and which resources remain restricted. This stage evaluates the consistency of access control rules implemented in the application and verifies whether discrepancies exist between assigned roles and effectively enforced permissions.
How this validation is structured

Evaluation of role-based access control

Identification of unauthorized access to restricted resources

User segregation testing

Parameter manipulation to verify privilege escalation

Analysis of data exposure between accounts
Direct impact

Identification of segregation failures between user roles

Exposure of unauthorized access to data and features

Foundation for reviewing authorization rules and access policies
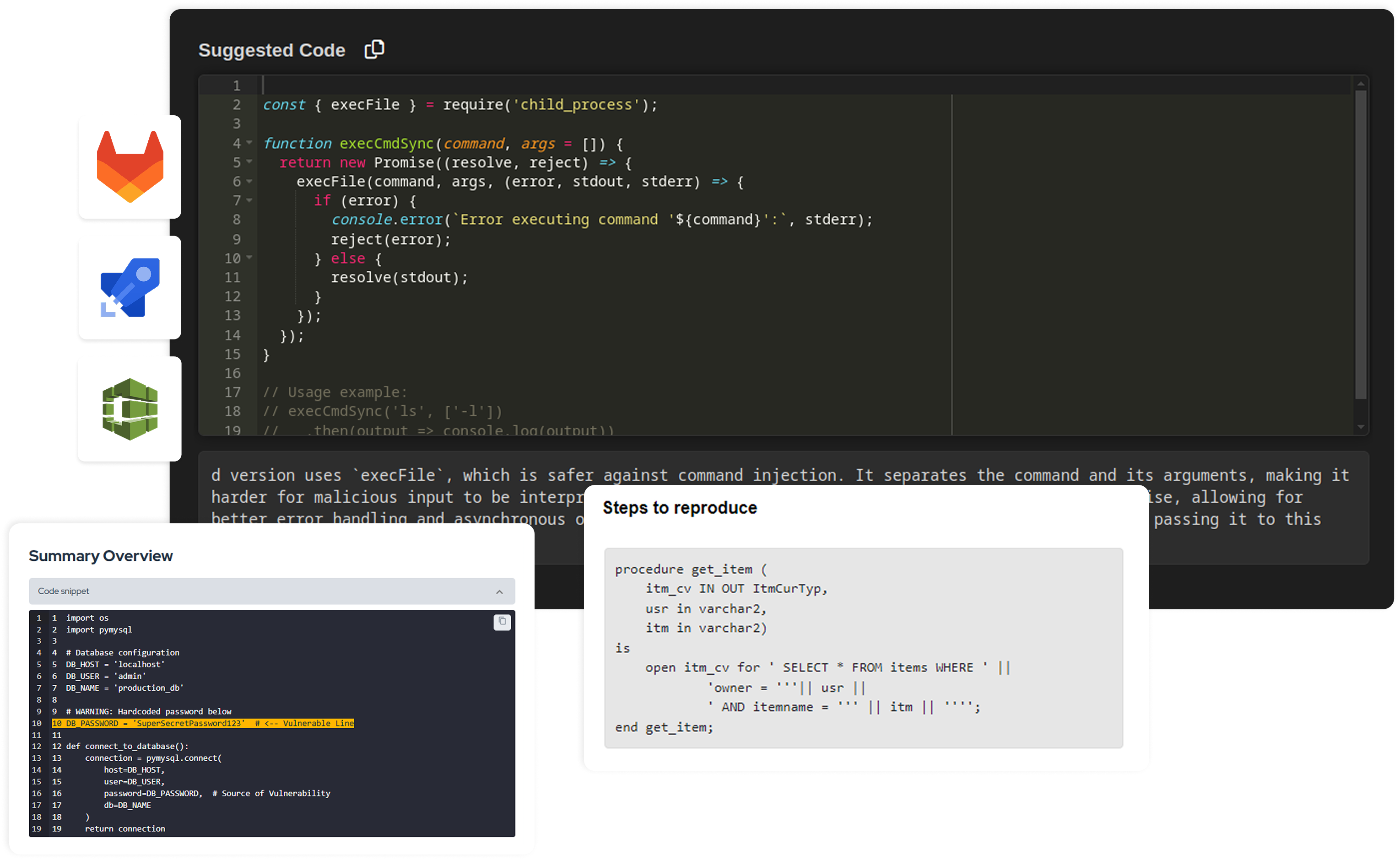
After mapping the surface and analyzing controls, Autonomous Pentesting attempts exploitation based on identified vectors. The objective is to verify whether vulnerabilities can be used to alter application behavior, access data, or perform actions outside the intended workflow.
We execute and validate vulnerabilities such as

Injections, including SQL Injection

Cross-Site Scripting (XSS)

Path Traversal

Parameter manipulation

Input validation failures

Unauthorized data exposure

Configuration weaknesses

Vulnerabilities associated with the OWASP Top 10
Direct impact

Practical confirmation of exploitability

Reproducible evidence

Risk-based prioritization
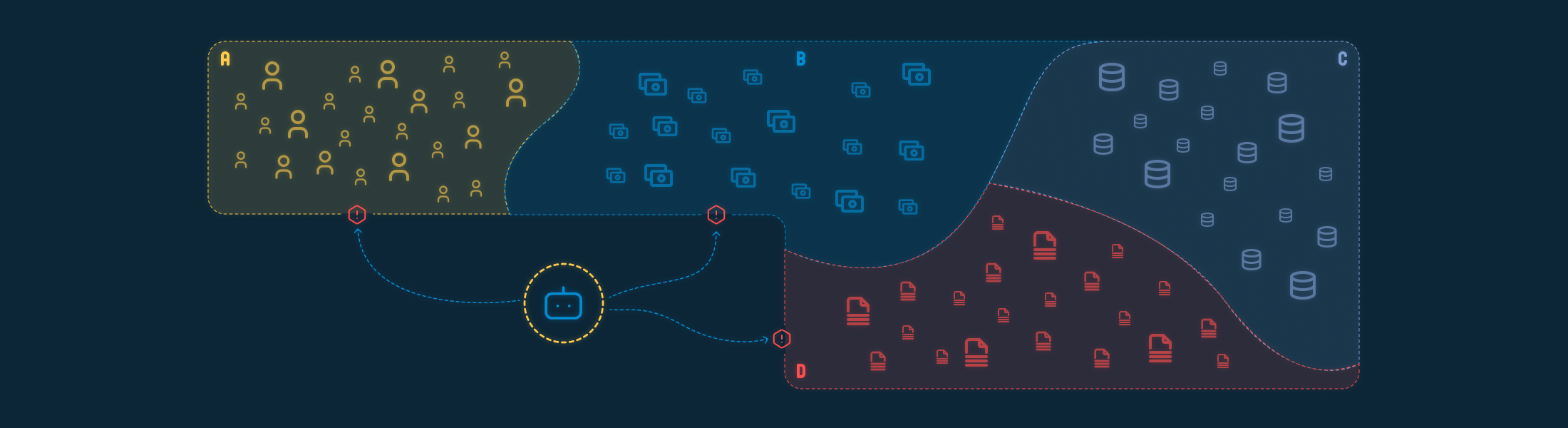
Isolated exploitation rarely represents the full scenario.
How chaining is structured

Connection between multiple vulnerabilities

Using one vulnerability as a starting point for another

Demonstration of real attack paths

Logical structuring of the exploitation flow
Direct impact

Confirmation of effective vulnerability exploitation

Structured record of the exploitation sequence

Prioritization based on observed impact during testing
Test execution considers the responses returned by the application at each interaction attempt. Blocks, status codes, error messages, and behavior variations influence the sequence of subsequent actions.
During execution

Continuous analysis of application responses

Dynamic adjustment of payloads

Modification of exploitation strategy

Prioritization of surfaces with greater impact potential
Direct impact

Behavior-driven coverage of the application

Identification of vectors that emerge from observed responses

Exploitation sequence adapted to the application context
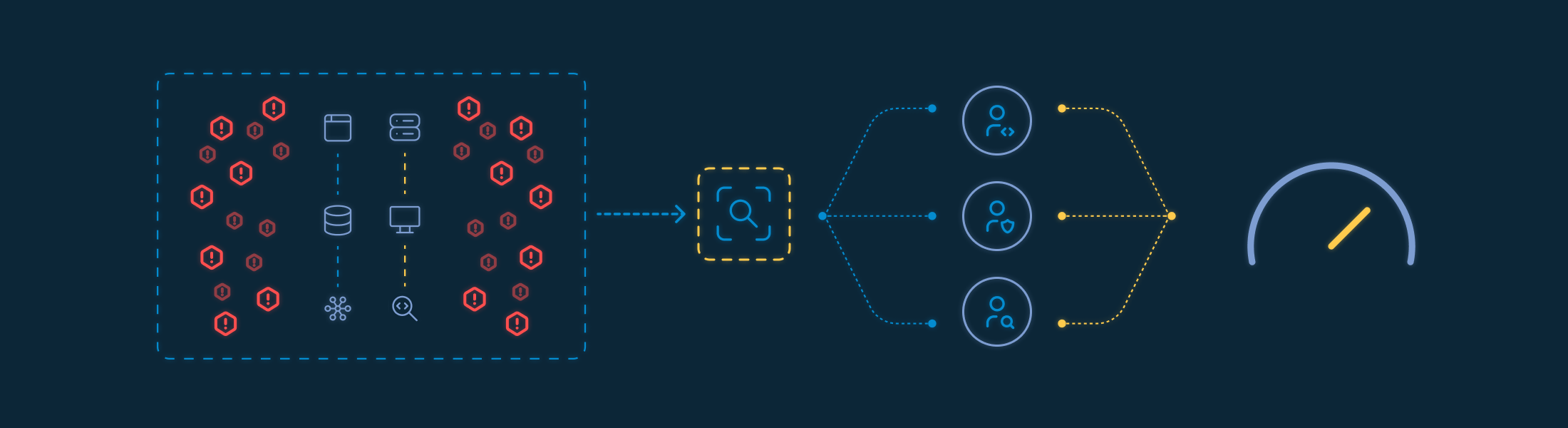
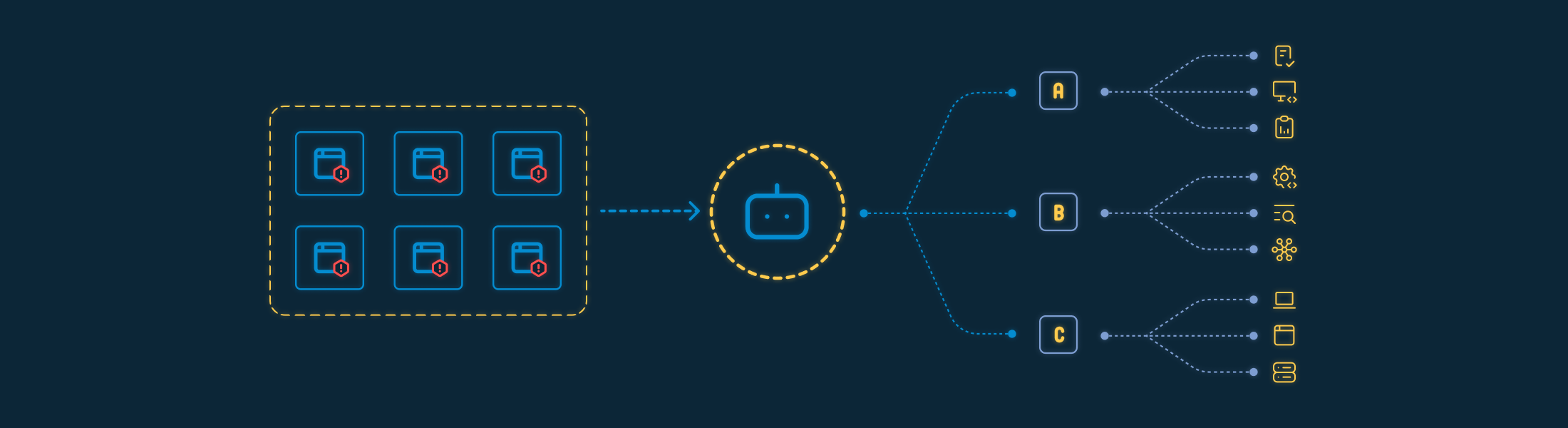
Each Autonomous Pentest execution is structured within the Conviso Platform, with a complete record of the evaluated scope, performed interactions, and confirmed vulnerabilities. The objective is to consolidate evidence, context, and traceability in a single workflow, enabling later analysis, remediation validation, and comparison between testing cycles.
Execution includes:
Platform-structured project with full description of the execution and scope context
List of identified vulnerabilities with severity classification and affected application or asset
Complete evidence including detailed requests and responses, payloads used, reproducible proof of concept, and executed exploitation sequence
Documented attack chain showing vulnerability chaining, structured exploitation flow, and amplified impact demonstration
Historical traceability with records of previous executions, comparison between cycles, and baseline for re-testing and remediation validation
Autonomous Pentest within the AI Autonomous AppSec Operation
The Autonomous Pentest integrates into your AppSec program and follows the evolution of your application. It performs exposed surface discovery, validates vulnerability exploitation, records complete evidence, and maintains cross-cycle history connected to the remediation workflow.
.svg)

.svg)
Conviso Platform for offensive security with AI and simulated attacks
The Conviso Platform centralizes pentest execution and result management. Exploited vulnerabilities, evidence, attack chains, and execution history are organized by application and connected to remediation workflows and risk evolution.
Talk to our specialists and see how to apply Autonomous Pentesting to your development lifecycle.
