PLATFORM OVERVIEW
Continuous evolution in AppSec, aligned with your business maturity
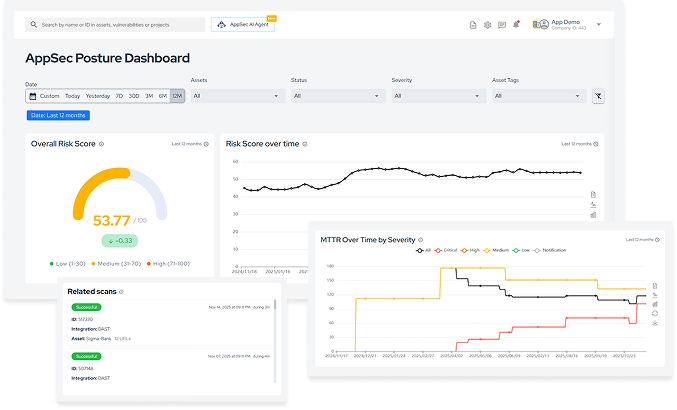
Conviso Platform is a complete application security risk management solution designed to centralize context, consolidate vulnerabilities, and operationalize AppSec programs at scale.

Application security as a continuous operation
Centralize risk, run tests, prioritize vulnerabilities, and automate remediation in a single platform.






Full AppSec operations powered by AI
Responsible for driving AppSec operational activities throughout the entire application development and operations lifecycle.
.svg)
.svg)
.svg)
.svg)
.svg)
.svg)
.svg)
.svg)
.svg)
 Discover the solution
Discover the solutionStructure, execute, and scale your AppSec program
.png)
.png)
.png)
.png)
Continuous, automated security built for developers
.png)
.png)
.png)
.png)
Technology, AI, and structured operations to scale your AppSec program

Modeled threats, code findings, dynamic testing, and pentesting operate within the same asset context.

Features evolve based on monitoring emerging vulnerabilities, new exploitation techniques, and changes in the development ecosystem.

AI analyzes security results from code, applications, and dependencies, prioritizes vulnerabilities based on asset criticality, executes automated remediation, detects reintroduced vulnerabilities after code changes, and performs autonomous pentesting with chained exploitation.

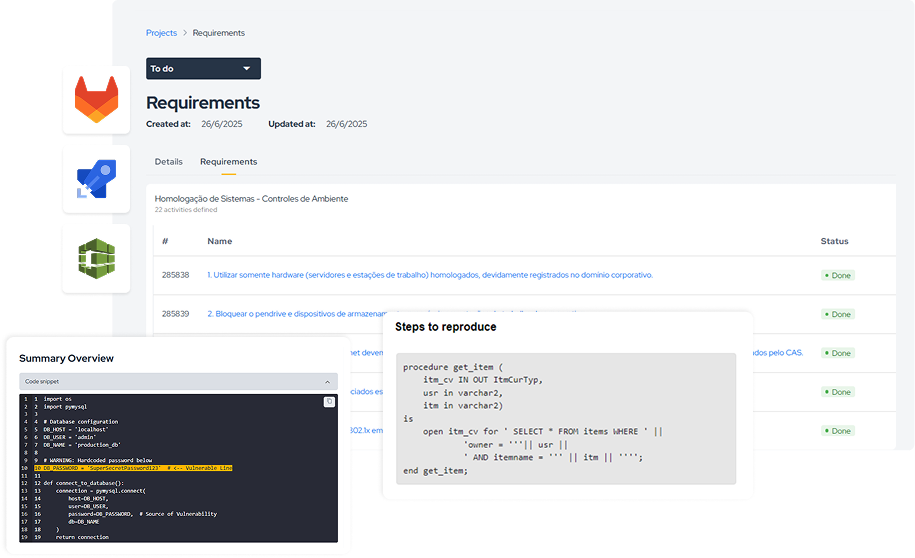
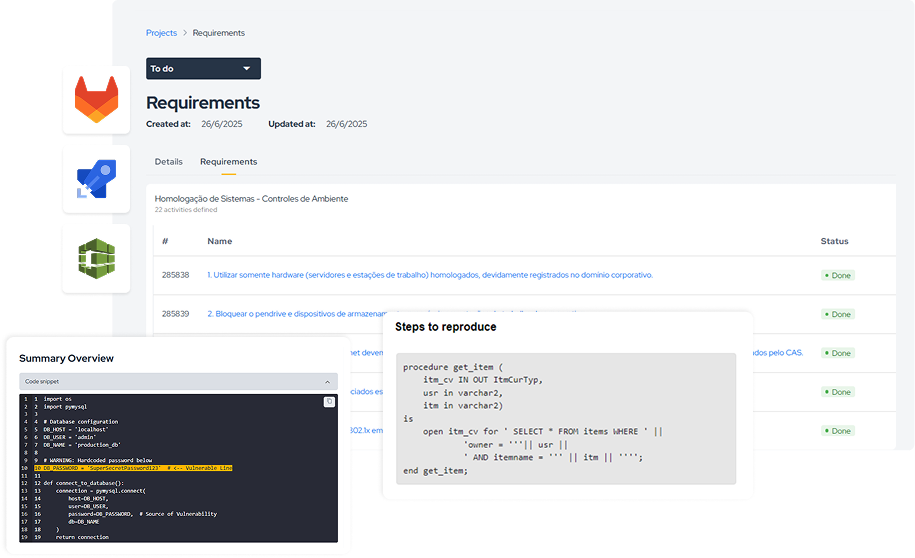
Pentest, Red Team, and PCI audit results are organized as scoped projects with assigned owners and tracked evidence, linking testing results directly to remediation.

The platform connects architectural threats with vulnerabilities identified in AST, DAST, and Pentest, showing threats, associated findings, and mitigation status within the same asset.

The platform automatically updates risk levels per asset and portfolio based on new commits, scans, CVEs, or exploitation evidence.
use case
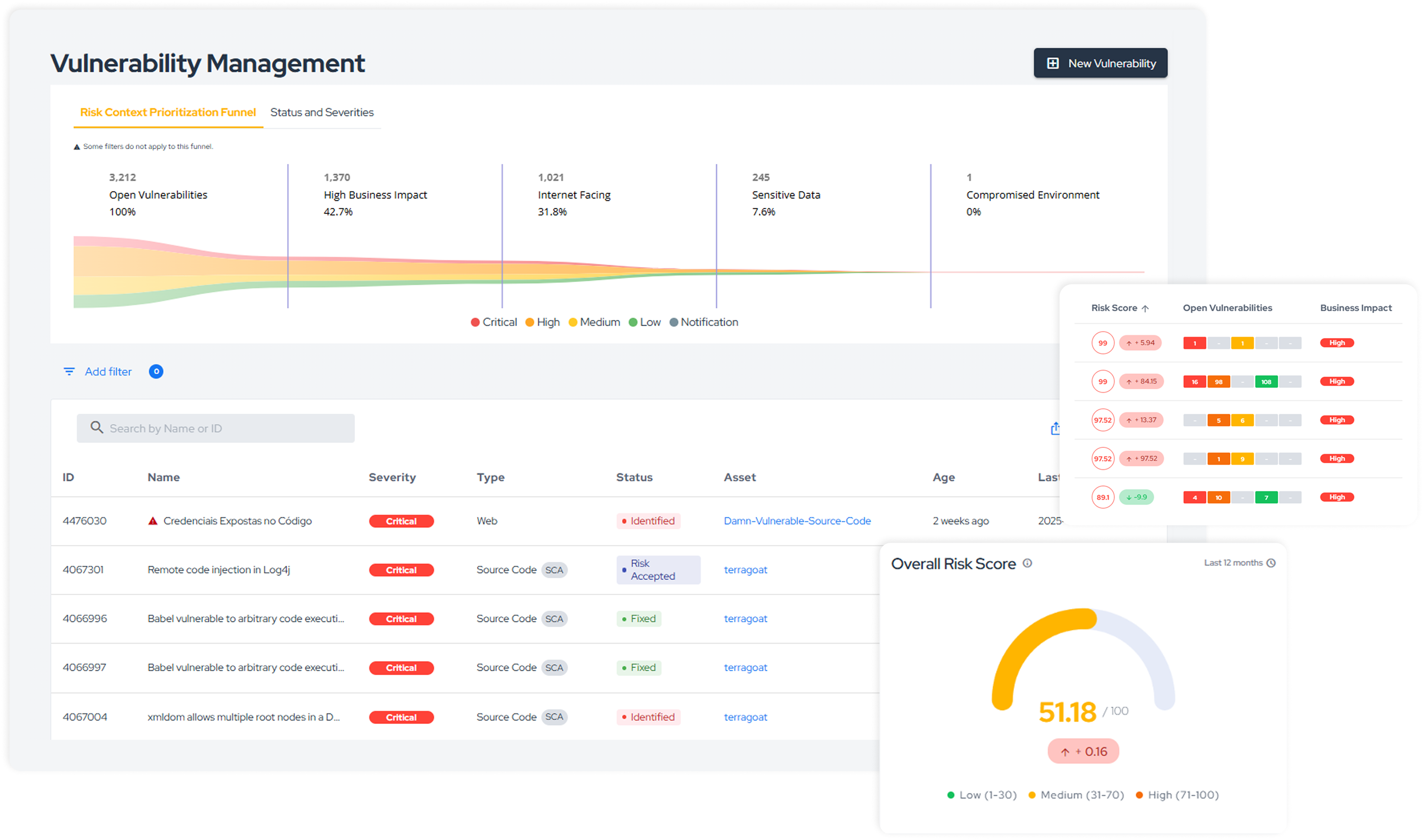
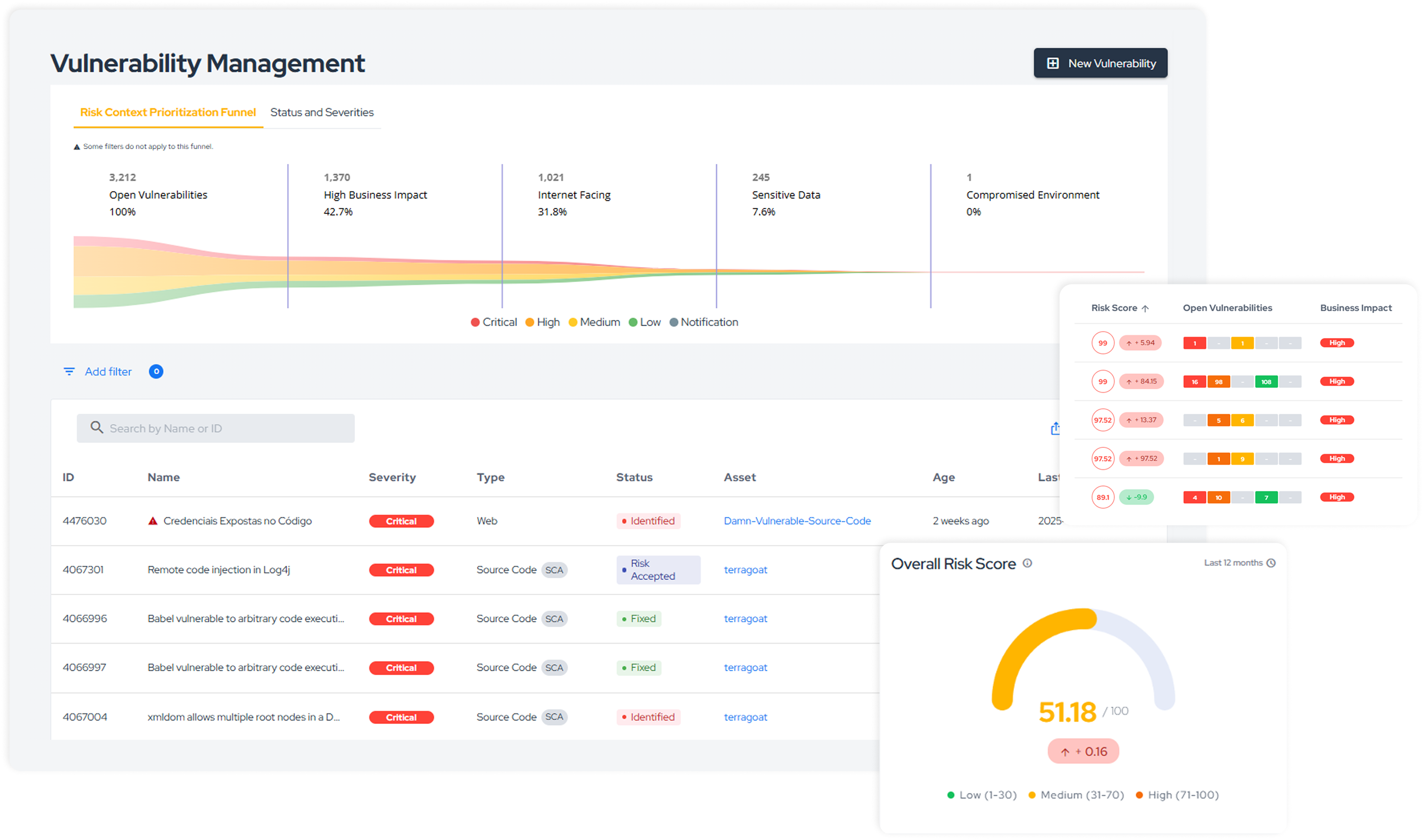
Unify AST, DAST, and SCA/SBOM results, eliminate duplicates, and prioritize remediation based on business impact.

Centralized correlation of vulnerabilities across applications, APIs, and components

Prioritization by exposure and criticality, with clear ownership per team

Evidence and status tracked in an auditable, end-to-end workflow
Explore Conviso Platform solutions and build your AppSec journey
Structured by products and add-ons, the platform allows companies to build their AppSec journey according to real needs, covering everything from secure design to active protection and regulatory compliance.
.png)
Web and API Protection
disponível apenas para usuários do plano Developers
Active edge protection with WAF and global CDN. Blocks real-time attacks while maintaining high performance in production.
Learn more>
AppSec Agent AI
disponível apenas para usuários do plano Developers
AI-powered agent integrated into IDEs, PRs, and pipelines. Detects flaws, suggests fixes, reviews code, and guides developers within their workflow.
Learn more>
.png)
ASPM
disponível apenas para usuários do plano Developers
Centralizes and orchestrates AppSec in a single platform, unifying scanners, prioritizing real risks, and providing end-to-end security visibility.
What is ASPM>

Vuln Intelligence
disponível apenas para usuários do plano Developers
Consolidates findings from multiple sources and applies real risk–based prioritization, reducing noise and accelerating decision-making.
Learn more>

AppSec Squads
disponível apenas para usuários do plano Developers
Specialized squads dedicated to operating and evolving AppSec programs. They structure processes, train teams, and elevate security maturity.
Learn more>

AppScan
disponível apenas para usuários do plano Developers
Automated security testing that transforms findings into traceable vulnerabilities, fully integrated into the development pipeline.
Learn more>

Web and API Scan
disponível apenas para usuários do plano Developers
Dynamic testing (DAST) for detecting vulnerabilities in applications and APIs, with direct integration into remediation workflows.

Threat Modeling
disponível apenas para usuários do plano Developers
Anticipates risks from the design phase, identifying threats and supporting secure decisions in architectures and application flows.
Saiba mais>

Supply Chain
disponível apenas para usuários do plano Developers
Complete visibility into software dependencies and components, with vulnerability analysis and third-party risk control.

OffSec Manager
disponível apenas para usuários do plano Developers
Organizes and tracks offensive testing with prioritized findings, risk visibility, and integration into the development lifecycle.

AppSec Manager
disponível apenas para usuários do plano Developers
Centralizes application security management, consolidates vulnerabilities, and structures workflows for risk control and prioritization.
Saiba mais>

PCI Manager
disponível apenas para usuários do plano Developers
Complete PCI DSS compliance management with structured controls, evidence, and reports for audits and continuous maintenance.
Integrations across the entire development lifecycle
Conviso Platform integrates code repositories, CI/CD pipelines, security scanners, and task management tools to connect security directly into the development workflow.



























Get your questions answered about Conviso Platform
We've selected the most common questions about our ASPM platform to help you understand how it fits into your AppSec program — from tool integration to compliance and maturity support.
Still have questions? Access our detailed documentation or chat with our team.
A Conviso recentemente adquiriu a N-Stalker, uma solução de DAST amplamente reconhecida no mercado global de segurança de aplicações, e a incorporou à sua plataforma. Isso permitiu a realização de análises dinâmicas por meio de uma solução própria.
Além disso, as análises de código estático (SAST) são conduzidas utilizando a engine do Nessus, que está integrada à nossa plataforma.
